AWS IAM
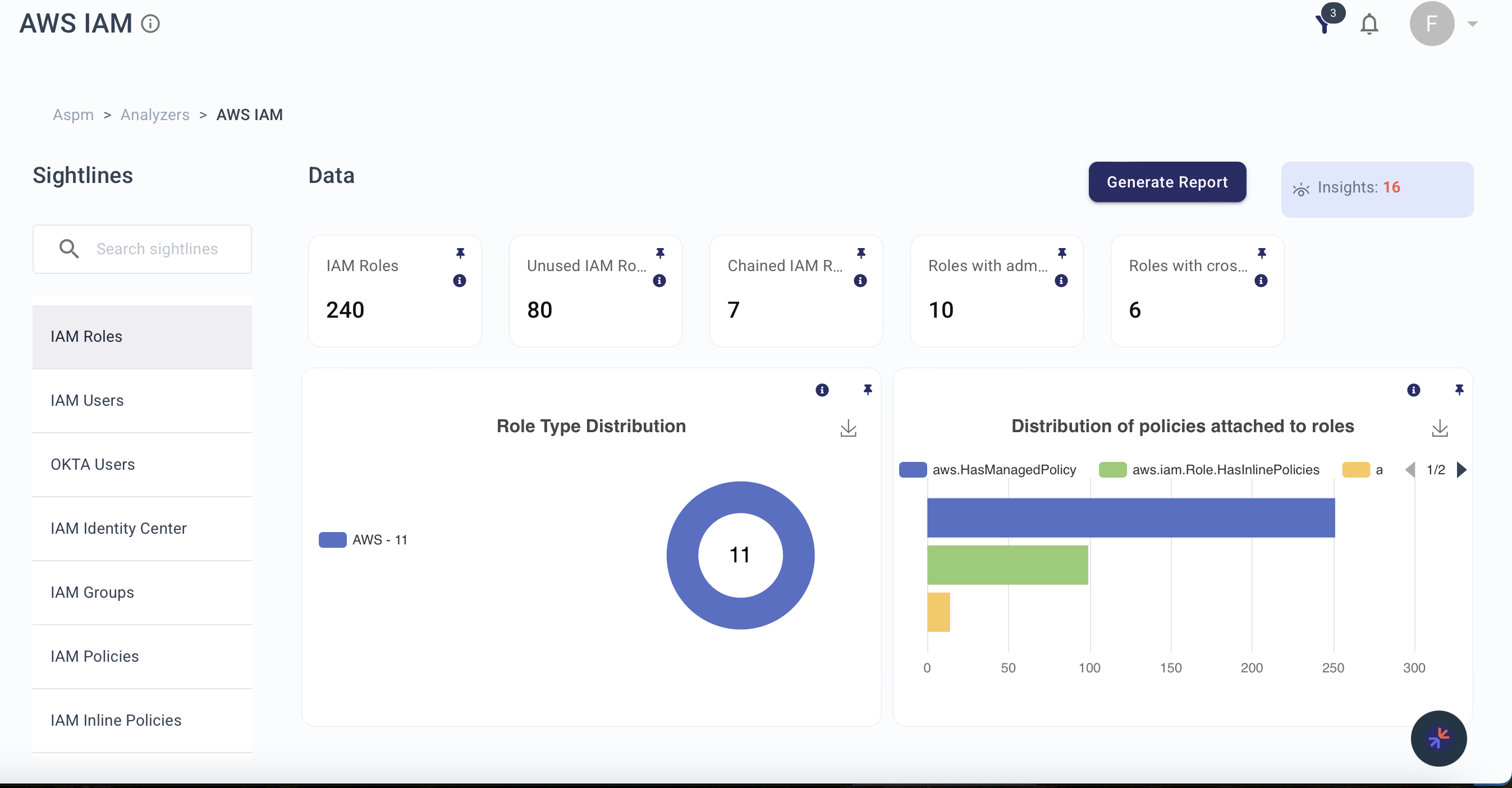
The AWS IAM Analyzer provides detailed insights into Identity and Access Management within your AWS environment. It helps identify excessive privileges, unused roles, cross-account access risks, and policy misconfigurations across users, groups, and roles.
Required Blueprints: AWS, Okta
Sightlines
| Sightline | Description |
|---|---|
| IAM Roles | Surfaces role usage, excessive permissions, admin access, and cross-account role configurations. |
| IAM Users | Provides visibility into users with excessive privileges, admin access, unused accounts, and MFA status. |
| IAM Identity Center | Monitors IAM Identity Center instances, users, and groups within centralized authentication, with region-based distri... |
| IAM Groups | Monitors group configurations, admin access, and policy associations. |
| IAM Policies | Tracks policy usage, admin access grants, wildcard permissions, and assume-role configurations. |
| IAM Inline Policies | Monitors inline policies attached to roles, users, or groups to ensure least privilege adherence. |
| IAM Password Policies | Ensures password configurations comply with security best practices such as the AWS CIS Foundations Benchmark. |
| IAM Access Keys | Provides visibility into access key status, rotation, usage trends, and users with unused keys. |
| IAM Policies for Storage | Monitors admin policies attached to storage services (S3, DynamoDB, RDS, Redshift). |
| IAM Policies for Streaming | Monitors admin policies attached to streaming services (SNS, Kinesis, SQS). |
| IAM Policies for Compute | Monitors admin policies attached to compute services (Lambda, ECS, EC2, ELB, ECR). |
| IAM Policies for CloudWatch | Monitors admin policies attached to CloudWatch and CloudWatch Logs resources. |
| IAM Users Password Policies | Monitors user password status, MFA compliance, and access denied events. |
| IAM Users Access Patterns | Surfaces user login and activity patterns including inactive users, cross-account access, and resource access history. |
| IAM Users Access Keys | Provides visibility into access key status per user, including dual keys, unused keys, and key distribution. |
| IAM Access to KMS | Tracks KMS access permissions across users, groups, and roles. |
| IAM Service-Linked Roles | Monitors service-linked roles to ensure only necessary permissions are granted. |
| IAM Across Systems | Tracks user permissions spread across various AWS services. |
| IAM Policy Impact Analysis | Identifies policies attached to resources and orphaned policies not attached to any resource. |
| IAM Access to CloudTrail | Monitors who has access to CloudTrail logs across users, groups, and roles. |
| IAM Managed Policies | Tracks managed policies and their adherence to the principle of least privilege. |
| User Impact Analysis | Provides a comprehensive view of user impact across the AWS environment, highlighting excessive permissions and unusu... |
Explorer Node Types
Use these node types in Explorer or KAI to query resources surfaced by this analyzer:
aws.iam.User, aws.iam.Role, aws.iam.Group, aws.iam.Policy, aws.iam.PolicyInline, aws.iam.AccessKey, aws.iam.PasswordPolicy, aws.identitystore.User, aws.identitystore.Group
Related Analyzers
- AWS Compute — EC2 instance profiles and IAM role associations
- AWS Storage — S3 bucket policies and IAM-based access control
- AWS RDS — Database IAM authentication
- AWS Network — VPC/subnet access controlled by IAM policies
- AWS Streaming — Admin policies on SNS, Kinesis, and SQS
Insight Feed Alerts
- Unauthorized Access Attempts: Flags suspicious login attempts such as failed login spikes or logins from unusual locations.
- Inactive Users Detected: Identifies accounts inactive for a set period that could be targets for attackers.
- Users Without MFA: Highlights users without multi-factor authentication enabled.
- Deprovisioned Users Activity: Monitors access attempts by deprovisioned users.
- Admin Role Misuse: Triggers on unusual activity related to users with administrative privileges.
- Unused IAM Roles: Identifies IAM roles not being actively used.
- IAM Roles with Wildcard Access: Flags roles granting wildcard access (e.g.,
"Action": "*"). - IAM Roles with Cross-Account Access: Flags roles with cross-account permissions that could enable privilege escalation.
- Expired IAM Passwords: Monitors users with expired passwords.
- Unrotated IAM Access Keys: Identifies access keys not rotated within a specified time frame.
- IAM Users with Weak Passwords: Flags users whose passwords do not meet security standards.
- Service Account with Admin Access: Identifies service accounts with excessive admin privileges.
- Users without Groups: Highlights users not assigned to any groups.
- Users with Admin Access: Flags users with direct admin access.
- Users with Unused Access Keys: Identifies users with access keys not used within a specified period.
- Users with Elevated Privileges via IAM Policies: Identifies users with overly permissive policy-based access.
- IAM Policies that Allow Wildcard Resource Access: Flags policies allowing wildcard access to resources.
- IAM Policies Attached to Critical Resources: Monitors policies granting admin access to critical resources.
- IAM Users with Inline Policies: Identifies users with inline policies that may provide excessive permissions.
- IAM Policies for High-Risk Resources: Identifies admin-level access policies for high-risk resources like S3, EC2, and Lambda.
- IAM Policies Allowing Cross-Service Role Assumption: Flags policies allowing cross-service role assumption.
- IAM Policies Violating Least Privilege Principle: Identifies policies granting unnecessary access.
- IAM Roles with Full Access to Sensitive Services: Identifies roles with full access to KMS, CloudTrail, or IAM.
- IAM Access to KMS: Monitors entities with direct or indirect access to AWS KMS.
- IAM Users with CloudTrail Access: Identifies users and groups with access to CloudTrail logs.
- IAM Users Accessing Unused Resources: Identifies users accessing unused or underutilized resources.
- IAM Roles with Broad Permissions: Identifies roles granting broad permissions across services.