aspm
Application Security Posture Management (ASPM)
The ASPM domain within Kscope KDefend secures your software supply chain — from code repositories and dependencies to container images and CI/CD pipelines. It aggregates findings from SAST, DAST, SCA, secrets scanning, and IaC analysis through the context graph to deliver prioritized, business-aware vulnerability management.
How It Works
- Application Blueprints ingest repository metadata, dependency trees, scan results, container manifests, and CI/CD configurations
- Context Graph maps relationships between repos, packages, applications, environments, and owners
- ASPM Analyzers correlate findings across code, dependencies, containers, and infrastructure-as-code
- Insight Feeds surface prioritized findings scored by business criticality and exploitability
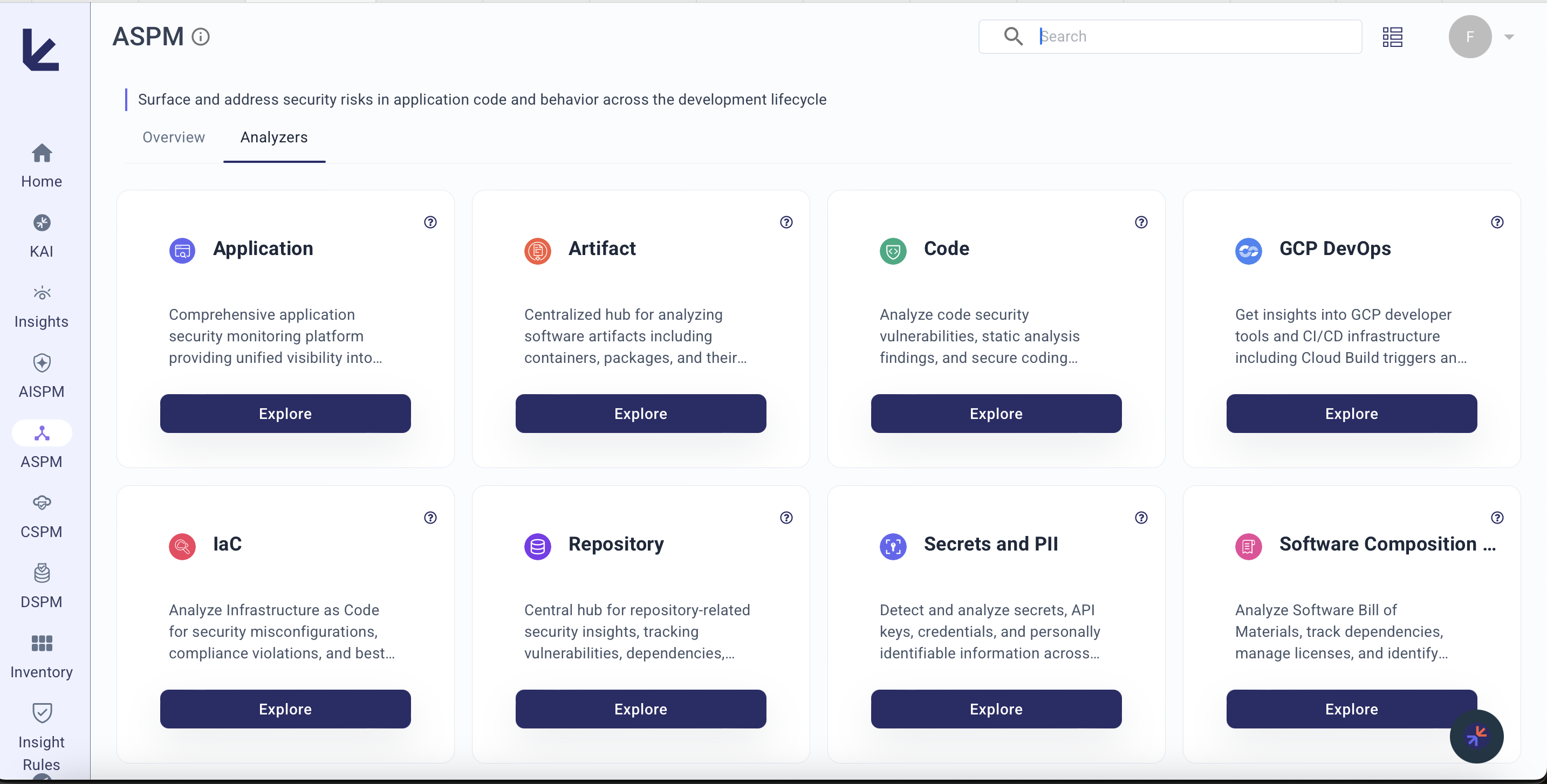
Analyzers
| Analyzer | What it covers | Blueprints |
|---|---|---|
| Application | Application-level risk scoring, security profile tracking, API vulnerability detection, DAST findings | GitHub, DAST, AI-DAST |
| Repository | Repository configurations, branch protection, 2FA enforcement, admin permissions, visibility settings | GitHub, Bitbucket |
| Code | Code-level vulnerability scanning (SAST), risk scoring per repository, production risk assessment | GitHub, Snyk, Checkmarx |
| Software Composition Analysis | Package dependencies, vulnerable packages, license compliance, SBOM analysis | SBOM, Snyk |
| Secrets and PII | Exposed API keys, passwords, tokens, and personally identifiable information in code and containers | GitHub |
| IaC | Infrastructure-as-code misconfigurations in Terraform, CloudFormation, and Kubernetes manifests | GitHub |
| Artifact | Container image vulnerabilities, base image risks, OS-level CVEs, container misconfigurations | GitHub |
| Engineering Operations | Pull request activity, commit patterns, repository throughput, net code changes | GitHub, Bitbucket |
| GCP DevOps | GCP Cloud Build, Artifact Registry, deployment pipelines, and DevOps security | GCP |
What It Detects
Code Vulnerabilities
- SAST findings across repositories, scored by production risk
- Repositories with high/critical vulnerabilities deployed to ECS, EKS, or container apps
- Top 10 riskiest repositories by production risk score
Dependency & Supply Chain Risks
- Vulnerable third-party packages with exploitability context
- Package version analysis and dependency impact mapping
- License policy violations across the software supply chain
- SBOM completeness and accuracy
Secrets & Sensitive Data
- Hardcoded API keys, passwords, and tokens in source code
- PII exposed in code repositories and container images
- Secret types distribution and remediation tracking
Infrastructure-as-Code
- Terraform, CloudFormation, and Kubernetes manifest misconfigurations
- IaC vulnerabilities by provider and severity
- Repositories with the highest IaC risk exposure
Container Security
- Container image vulnerabilities from OS packages, user code, and base images
- Container misconfigurations and security posture
- Top 10 riskiest containers by package vulnerability count
Repository Posture
- Repositories without default branch protection
- Organizations missing 2FA enforcement
- Repositories allowing unsigned commits
- Shell injection risks in GitHub Actions
Key Metrics
| Metric | Description |
|---|---|
| Apps Protecting | Total applications monitored across all environments |
| Vulnerable Repos | Repositories with unresolved high/critical vulnerabilities |
| Total Vulnerabilities | Aggregate count across code, dependencies, containers, and IaC |
| MTTR | Mean time to remediate across vulnerability categories |
| Pipeline Coverage | Percentage of pipelines with active security scanning |
| ASPM Security Risk Score | Composite 0–100 score dynamically weighted across all active ASPM analyzers. Only analyzers with a configured blueprint contribute to the score. |