Artifact
The Artifact Analyzer specializes in analyzing container images and their security posture across your software delivery pipeline. It helps teams identify, assess, and remediate security risks in container artifacts.
Required Blueprints: GitHub, Azure DevOps, Azure, Bitbucket, AWS, Wiz
Sightlines
| Sightline | Description |
|---|---|
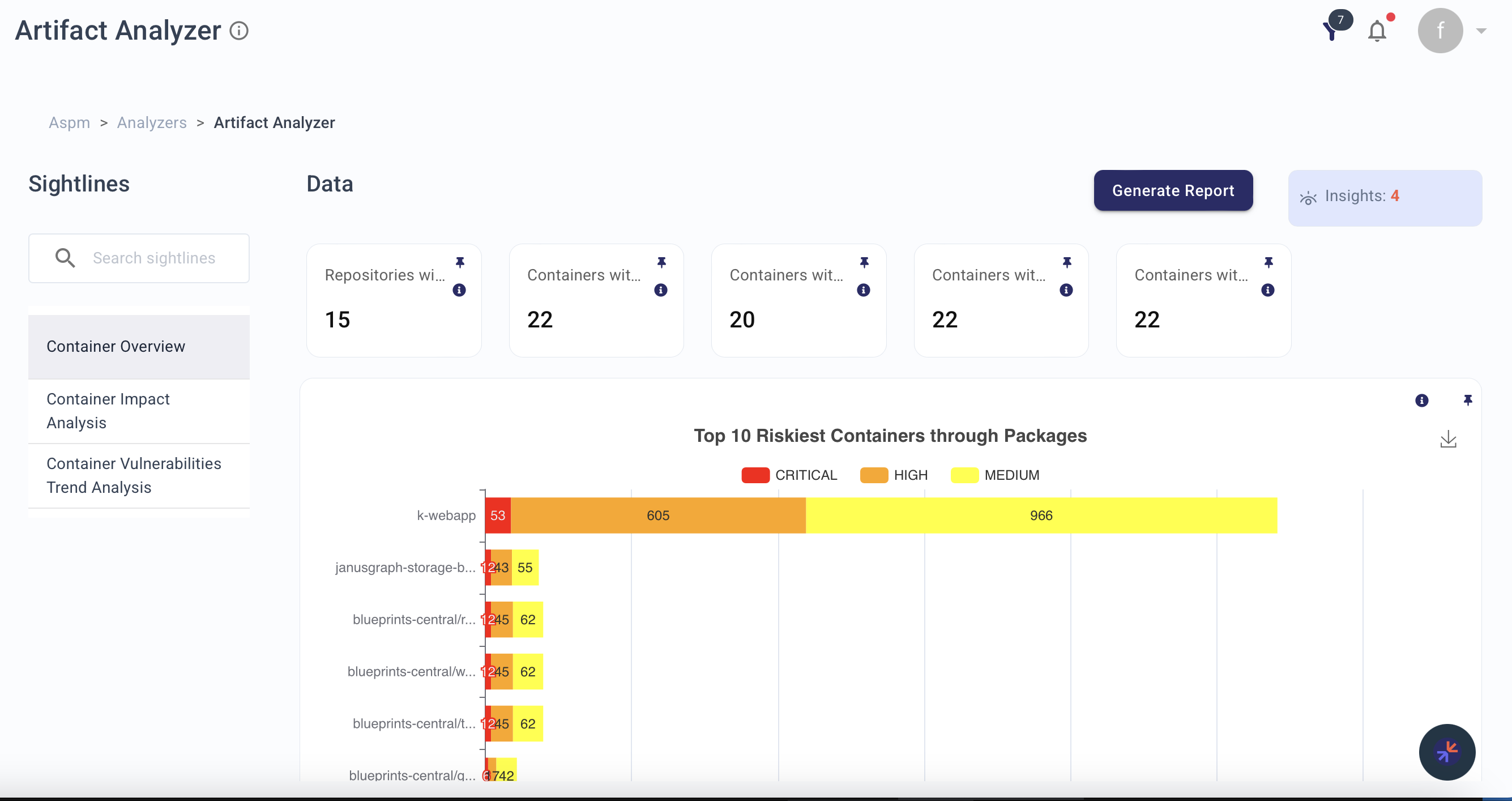
| Container Overview | Comprehensive visibility into container security, identifying vulnerabilities and highlighting the riskiest container... |
| Container Impact Analysis | Assesses the impact of vulnerabilities in container images and guides decision-making for containerized environments. |
| Container Vulnerabilities Trend Analysis | Monitors trends in container vulnerabilities, enabling proactive risk mitigation. |
| Vulnerability Impact Analysis | Detailed assessment of how specific vulnerabilities affect your containerized environment, helping prioritize remedia... |
Explorer Node Types
Use these node types in Explorer or KAI to query resources surfaced by this analyzer:
aws.ecr.Repository, aws.ecr.Image, aws.ecr.ImageScanFinding, azure.containerregistry.Registry, azure.containerregistry.Image, github.ghcr.Package
Related Analyzers
- Software Composition Analysis — Package vulnerabilities in container images
- Code — Built artifact security from source code
- Repository — Source repositories linked to container registries
- Engineering Operations — CI/CD artifact production pipelines
Insight Feed Alerts
Container Critical Vulnerability
Notifies about critical vulnerabilities detected in containers, enabling swift action to address critical security risks.
Container High Vulnerability
Provides insights into high-severity container vulnerabilities, supporting proactive risk management.
Container Medium Vulnerability
Highlights medium-severity vulnerabilities in containers, helping teams prioritize moderate security risks.
Container Low Vulnerability
Identifies low-severity vulnerabilities in containers, ensuring comprehensive visibility for long-term improvements.
Vulnerable dependency (CVE) in container from Operating System
Identifies security vulnerabilities originating from OS-level packages within containers, enabling targeted patching of foundational components.
Container Security Misconfigurations
Identifies security configuration issues in container images and Dockerfiles, including privilege escalation risks, exposed ports, and insecure defaults.