cspm
Cloud Security Posture Management (CSPM)
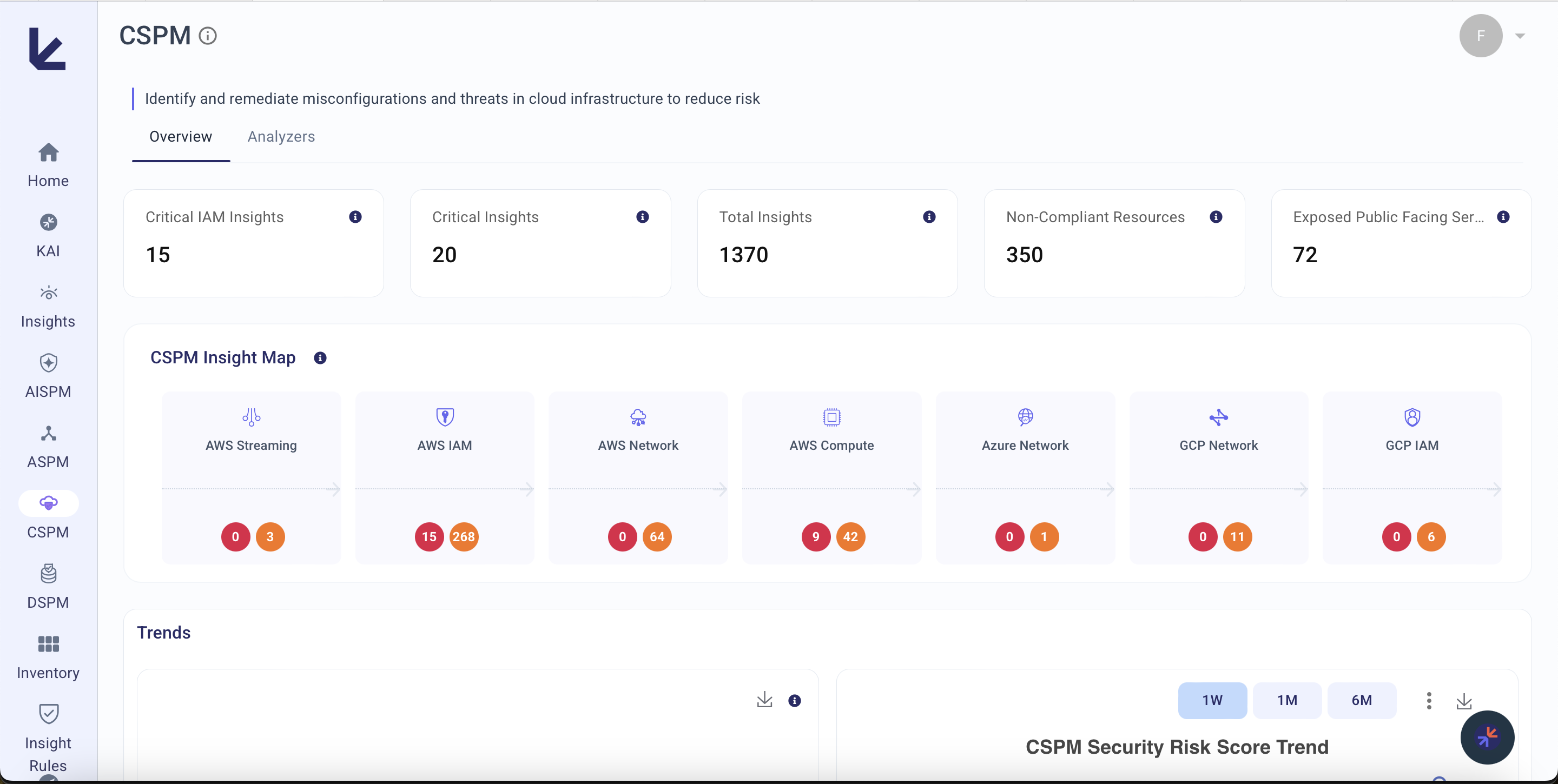
The CSPM domain within Kscope KDefend provides continuous monitoring and analysis of your cloud infrastructure security posture across AWS, Azure, and GCP. It detects misconfigurations, IAM risks, network exposure, and compliance violations by correlating data from cloud Blueprints through the context graph.
How It Works
- Cloud Blueprints ingest infrastructure metadata — IAM policies, compute instances, network configurations, security groups — using read-only credentials
- Context Graph stores and correlates relationships across accounts, regions, and providers
- CSPM Analyzers detect misconfigurations, excessive permissions, and compliance violations
- Insight Feeds surface prioritized findings scored by business impact and exploitability
Analyzers
| Analyzer | What it covers | Blueprints |
|---|---|---|
| AWS IAM | IAM users, roles, policies, access keys, MFA compliance, cross-account access, least privilege violations | AWS |
| AWS Compute | EC2 instances, ECS clusters, Lambda functions, security groups, public exposure, AMIs | AWS |
| AWS Network | VPCs, subnets, Route 53, load balancers, security groups, NACLs, CloudFront, API Gateway | AWS |
| AWS Streaming | Kinesis streams and streaming infrastructure | AWS |
| Azure IAM | Azure AD roles and access management | Azure |
| Azure Network | VNets, DNS, VPN configurations, NSGs | Azure |
| GCP IAM | Service accounts, IAM roles, policy bindings | GCP |
| GCP Compute | Compute Engine instances and workloads | GCP |
| GCP Network | VPCs, firewall rules, networking infrastructure | GCP |
| Kubernetes | Cluster state, nodes, pods, RBAC, network policies, container security | Kubernetes |
| Azure Streaming | Azure streaming and event infrastructure security | Azure |
What It Detects
Identity & Access Risks
- IAM users with console access but no MFA enabled
- Roles with admin access or wildcard resource permissions
- Unused access keys, unrotated credentials
- Cross-account role trust misconfigurations
- Service accounts with excessive permissions
Network Exposure
- Security groups allowing unrestricted inbound access
- Public subnets with risky NACLs
- Publicly accessible EC2 instances without justification
- VPCs without private subnets
- Load balancers with insecure configurations
Compute Misconfigurations
- EC2 instances exposing non-public S3 buckets
- Lambda functions with deprecated runtimes
- ECS clusters with insufficient security configurations
- Unused key pairs and detached elastic IPs
Compliance Posture
- CIS Benchmark violations for AWS, Azure, and GCP
- Drift from organizational security policies
- Password policies not meeting security standards
Key Metrics
| Metric | Description |
|---|---|
| Total Cloud Assets | Number of monitored cloud resources across all providers |
| Critical Misconfigurations | Count of high-severity configuration violations |
| IAM Risk Score | Composite score reflecting identity and access exposure |
| Network Exposure Score | Measure of publicly accessible attack surface |
| Compliance Coverage | Percentage of assets meeting defined security benchmarks |
| CSPM Security Risk Score | Composite 0–100 score dynamically weighted across all active CSPM analyzers. Only analyzers with a configured blueprint contribute to the score. |