dspm
Data Security Posture Management (DSPM)
The DSPM domain within Kscope KDefend monitors and protects your data stores — S3 buckets, RDS instances, and databases — by detecting encryption gaps, access misconfigurations, and public exposure risks. It correlates storage and database findings through the context graph to surface data security insights with business context.
How It Works
- Data Blueprints ingest metadata from S3, RDS, and direct database connections using read-only credentials
- Context Graph maps storage objects, database schemas, access policies, and IAM relationships
- DSPM Analyzers detect encryption gaps, public exposure, and excessive access patterns
- Insight Feeds surface prioritized findings scored by data sensitivity and business impact
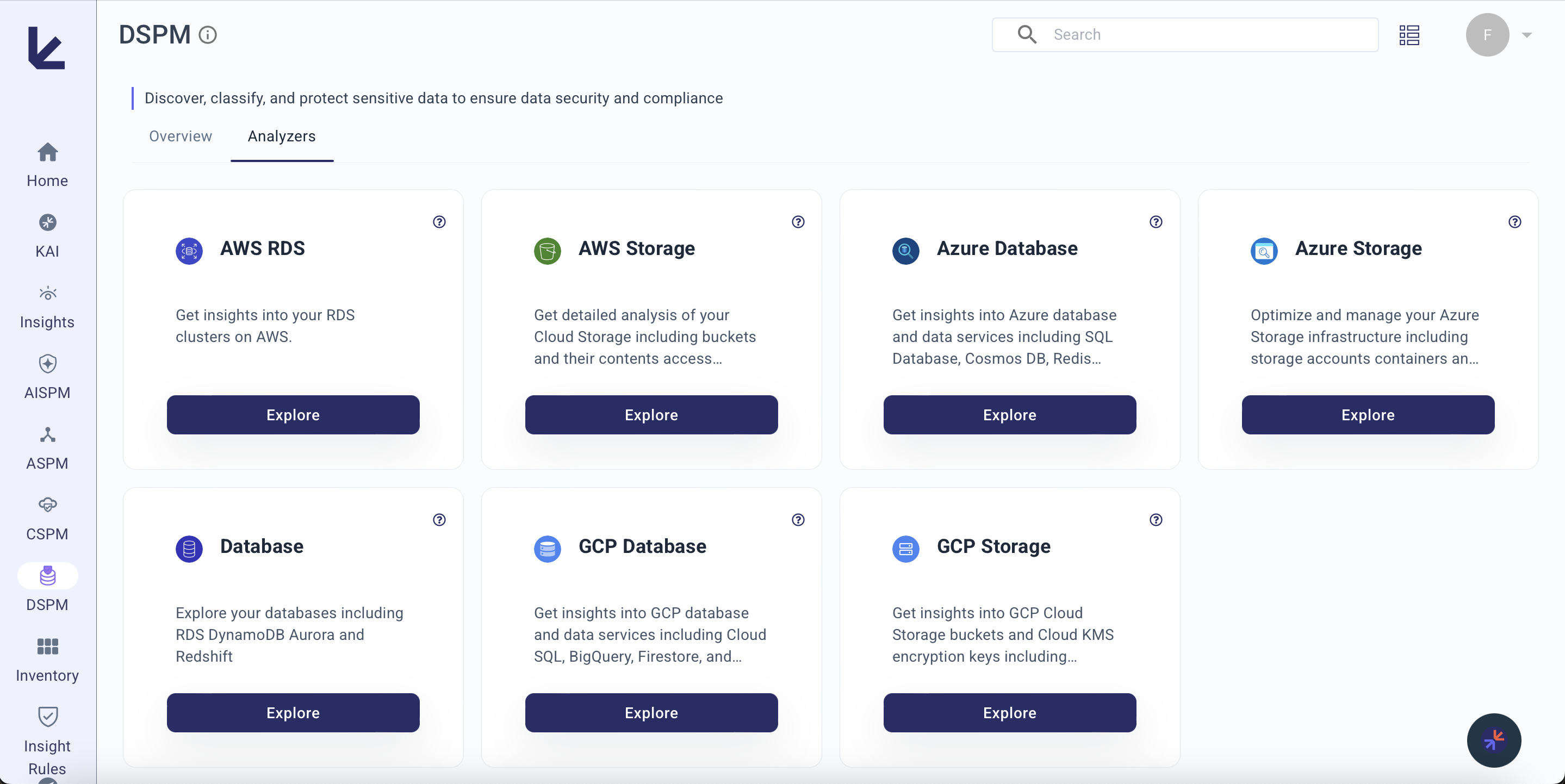
Analyzers
| Analyzer | What it covers | Blueprints |
|---|---|---|
| AWS Storage | S3 buckets — encryption, public access, versioning, logging, IAM policies, embedded policies, CloudTrail access events, EBS volumes and snapshots | AWS |
| AWS RDS | RDS instances — storage encryption, SSL/TLS enforcement, IAM authentication, security groups, snapshot encryption | AWS |
| Database | Direct database environments — tables, schemas, users, views, access patterns, admin privileges | Database |
| Azure Storage | Azure storage accounts, containers, encryption, access policies, replication, static site hosting | Azure |
| Azure Database | Azure database services — SQL Database, Cosmos DB, access controls, encryption | Azure |
| GCP Storage | GCP Cloud Storage buckets — access controls, encryption, lifecycle policies | GCP |
| GCP Database | GCP database services — Cloud SQL, Spanner, Firestore security and access | GCP |
What It Detects
Encryption Validation
- S3 buckets without server-side encryption
- RDS instances with storage encryption disabled
- Unencrypted EBS snapshots (publicly or privately shared)
- Missing KMS key configurations
Public Exposure Prevention
- S3 buckets with public access or permissive ACLs
- Buckets whose objects can be made public
- RDS instances with unrestricted security group access
- Publicly shared EBS snapshots
Access Misconfiguration
- IAM policies granting full S3 access (read/write/delete)
- Users with direct bucket access bypassing role-based controls
- EC2 instances exposing non-public S3 buckets to the internet
- Federated users with direct S3 access via assumed roles
- Database admin users with excessive privileges
Storage Hygiene
- Buckets without versioning or server access logging
- Unused or never-accessed buckets consuming storage
- Buckets without embedded or IAM policies
- Empty database tables and unused schemas
Key Metrics
| Metric | Description |
|---|---|
| Total Data Assets | S3 buckets, RDS instances, and database environments monitored |
| Unencrypted Storage | Count of storage resources missing encryption at rest |
| Public Exposure | Number of publicly accessible buckets, snapshots, or database endpoints |
| Access Violations | Users or roles with excessive data access permissions |
| Data Volume | Total data under management across monitored stores |
| DSPM Security Risk Score | Composite 0–100 score dynamically weighted across all active DSPM analyzers. Only analyzers with a configured blueprint contribute to the score. |
Key Sightlines
- S3 Bucket Security Distribution — Encryption, versioning, and public access status across all buckets
- RDS Encryption Compliance — Storage encryption distribution across database instances
- User Access to S3 — Which users access which buckets, and through what mechanisms (direct, IAM, inline, EC2)
- EBS Snapshot Exposure — Public vs private vs unencrypted snapshot counts
- Database User Privilege Map — Admin users, schema access, and table ownership across database environments