AWS Compliance
Analyzer: AWS Compliance
The AWS Compliance Analyzer offers comprehensive insights into the security and compliance of AWS accounts hosting Symframe infrastructure and applications. It assists IT Operations (IT Ops) and Security Operations (Sec Ops) engineers by automating compliance assessments, identifying misconfigurations, and ensuring adherence to security and operational best practices.
From a security perspective, the analyzer highlights potential vulnerabilities, such as public access configurations, insecure policies, and misconfigured access controls. For compliance, it ensures resources meet regulatory and organizational standards. In terms of operational observability, it provides insights that help optimize performance, improve security postures, and streamline resource management.
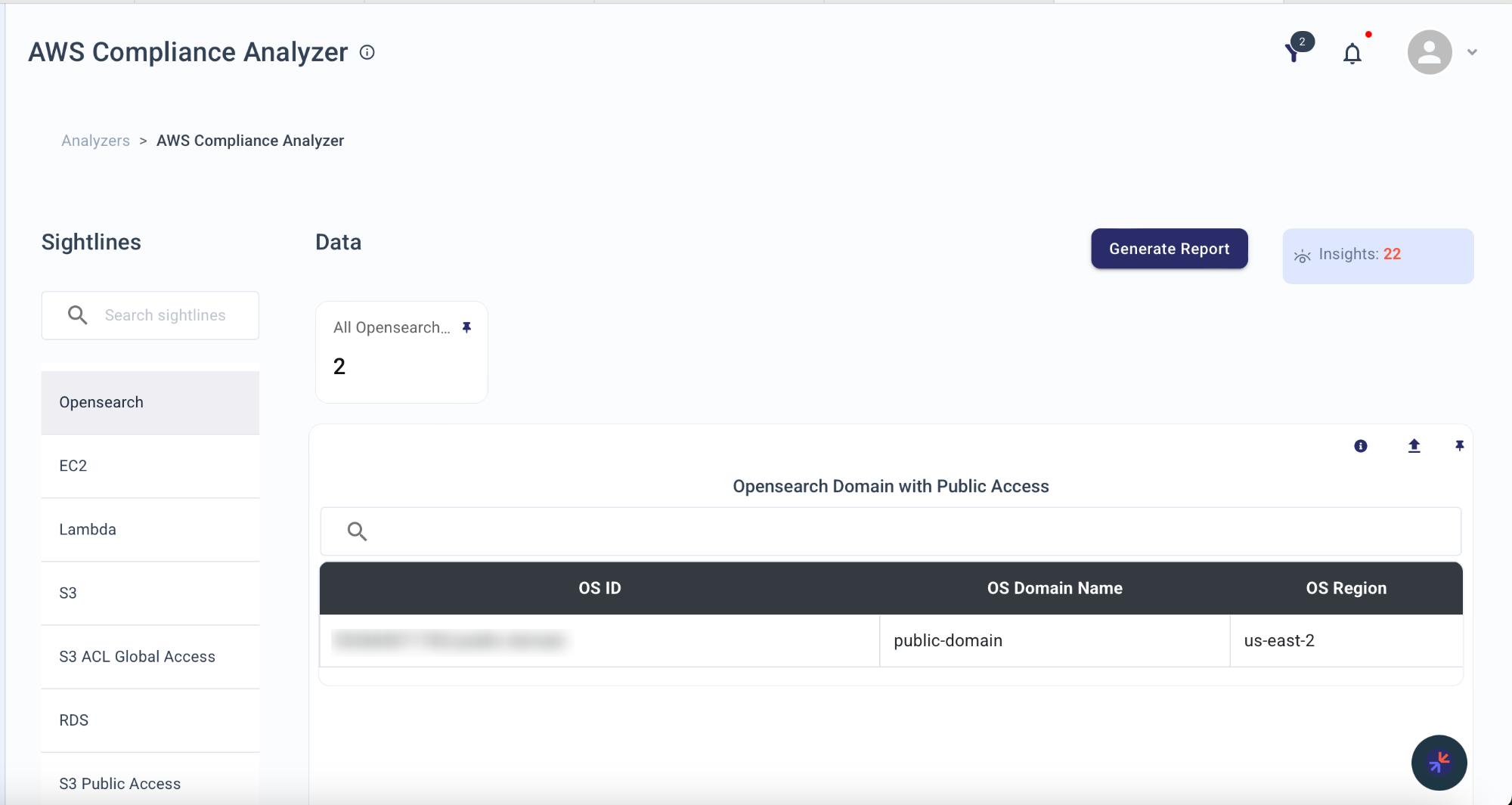
Sightlines
| Sightline | Description |
|---|---|
| Opensearch | The Opensearch sightline evaluates the security and accessibility of Opensearch domains. It provides IT Ops and S... |
| EC2 | The EC2 sightline monitors instance configurations for security vulnerabilities and operational inefficiencies. I... |
| Lambda | The Lambda sightline focuses on identifying insecure configurations and excessive privileges in Lambda functions.... |
| S3 | The S3 sightline examines bucket policies to identify public access and overly permissive actions. This helps Sec... |
| S3 ACL Global Access | The S3 ACL Global Access sightline analyzes ACL configurations to detect buckets exposed to global read or write ... |
| RDS | The RDS sightline identifies security and operational risks in relational database service instances. It provides... |
| S3 Public Access | The S3 Public Access sightline evaluates bucket-level settings to detect public access vulnerabilities. This ensu... |
| VPC Remote Services Access | The VPC Remote Services Access sightline identifies security groups that allow unrestricted remote service access... |
| VPC Application Services Access | The VPC Application Services Access sightline monitors security group configurations that control access to appli... |
| VPC Database Services Access | The VPC Database Services Access sightline evaluates security groups to ensure database service access configurat... |
| VPC Communication Services Access | The VPC Communication Services Access sightline identifies risks in communication protocol access. This helps IT ... |
| VPC Data Services Access | The VPC Data Services Access sightline analyzes security group configurations for data service access. It helps I... |
| VPC Directory Services Access | The VPC Directory Services Access sightline ensures the security of directory service access. It helps IT Ops and... |
| VPC Restricted Protocol and Database Access | The VPC Restricted Protocol and Database Access sightline identifies unrestricted access to sensitive protocols a... |
| IAM | The IAM sightline highlights overly permissive identity and access management (IAM) configurations. It helps IT O... |
| Cognito Identity Pool | The Cognito Identity Pool sightline identifies insecure configurations in Cognito identity pools. It helps IT Ops... |
| Redshift | The Redshift sightline evaluates Redshift cluster configurations for public access and encryption. It helps IT Op... |
| WAF | The WAF Sightline sightline evaluates Web Application Firewall (WAF) configurations by focusing on two key areas:... |