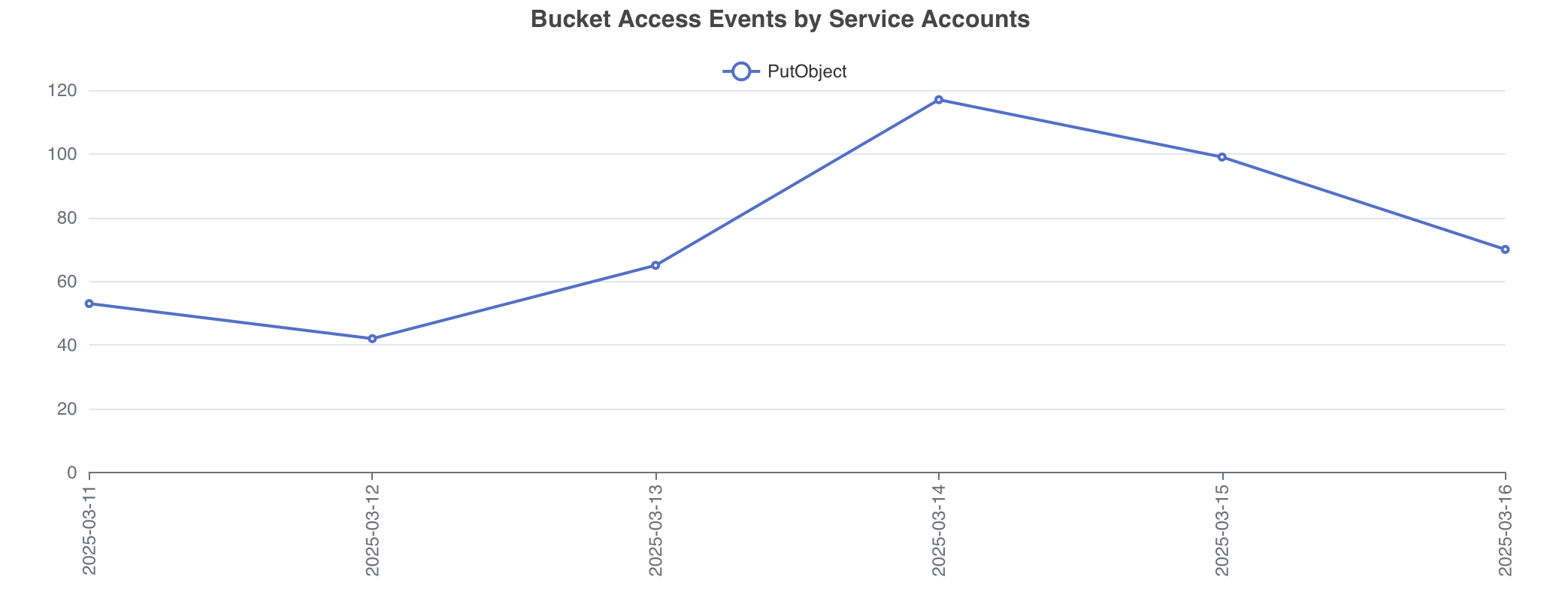
Bucket Access by Service Accounts Trend
Overview
The Bucket Access by Service Accounts Trend provides a historical analysis of how service accounts interact with cloud storage buckets. It highlights patterns, irregularities, and changes in access frequency by service accounts, enabling informed decision-making for both IT and security operations.
Why It Matters
-
Access Transparency:
- Identify which service accounts are actively accessing buckets and monitor changes over time.
- Detect trends in access patterns to ensure alignment with operational requirements.
-
Security and Risk Management:
- Monitor unusual access patterns or spikes in activity by service accounts to flag potential security issues.
- Reduce attack surface by identifying and restricting unnecessary access to buckets.
-
Compliance and Audit Readiness:
- Ensure that access by service accounts adheres to the principle of least privilege.
- Maintain detailed logs and trends for regulatory compliance and audits.
Key Use Cases
- Anomaly Detection: Identify irregular access patterns that might indicate compromised service accounts or misconfigurations.
- Policy Enforcement: Ensure that service accounts accessing buckets have permissions that match their intended purpose.
- Optimization of Access Policies: Use trend analysis to refine access policies for service accounts.
How IT and Security Engineers Benefit
IT Engineers:
-
Operational Insights:
- Understand which buckets are critical to application workflows by analyzing access trends of associated service accounts.
- Gain clarity on service account dependencies to prevent disruptions during policy updates.
-
Improved Resource Allocation:
- Eliminate redundant service accounts or reassign workloads for better resource utilization.
Security Engineers:
-
Proactive Threat Detection:
- Detect unauthorized access attempts by tracking unusual spikes or declines in service account activities.
- Quickly identify and mitigate potential insider threats or credential leaks.
-
Enhanced Compliance:
- Maintain a clear history of service account activities to meet compliance requirements.
- Prove adherence to access control policies during audits.
Implementation Steps
-
Enable Logging:
- Activate bucket access logs in your cloud environment (e.g., AWS CloudTrail, GCP Audit Logs, Azure Monitor).
- Ensure logs include service account identities.
-
Aggregate and Analyze Data:
- Use tools like AWS Athena, Google BigQuery, or Azure Log Analytics to query access logs.
- Visualize trends using dashboards in platforms like Datadog, Grafana, or Cloud-native monitoring solutions.
-
Set Alerts for Anomalies:
- Implement automated alerts for unusual service account behaviors (e.g., accessing buckets outside of usual hours).
-
Review and Refine Policies:
- Regularly audit permissions of service accounts accessing buckets.
- Revoke permissions for inactive or unnecessary service accounts.
Best Practices
-
Principle of Least Privilege:
- Ensure service accounts have only the permissions necessary for their tasks.
-
Regular Access Reviews:
- Periodically review service account access trends to identify outdated or excessive permissions.
-
Automated Monitoring:
- Use automated tools to continuously monitor and flag suspicious activity.
Tools and Technologies
- AWS: AWS CloudTrail, AWS Config, AWS IAM Access Analyzer
- Google Cloud: GCP Audit Logs, Cloud IAM, Cloud Monitoring
- Microsoft Azure: Azure Monitor, Azure Active Directory Logs
- Third-party Tools: Splunk, Datadog, or custom scripts for deeper analysis
Conclusion
Tracking the trend of bucket access by service accounts is a crucial practice for both IT and Security Engineers. By maintaining a clear understanding of how service accounts interact with storage resources, organizations can enhance security, optimize operations, and meet compliance requirements.
Generated by AI Assistant