| Definition | Data events capture object-level API activity (e.g., S3 object access, Lambda function invocation). |
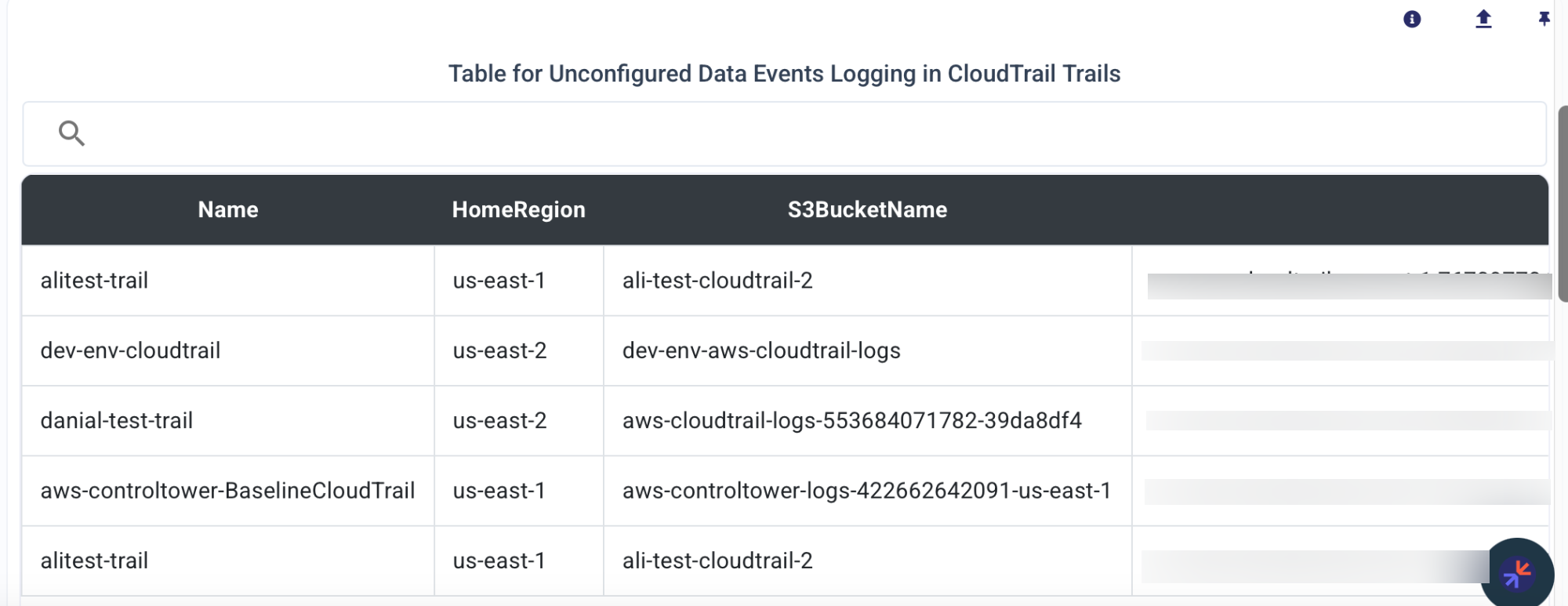
| Unconfigured Logging | When data events logging is not enabled, CloudTrail does not log these activities. |
| Risks | Lack of visibility into data access, potential undetected unauthorized or malicious activities. |
| Impacted Services | AWS S3, AWS Lambda, DynamoDB, and other services with object-level APIs. |
| Key Indicators | Absence of specific logs for actions like GetObject, PutObject, or InvokeFunction. |
| Mitigation Steps | Enable data events logging in CloudTrail for the relevant trails. |
| Configuration Steps | 1. Open CloudTrail console. 2. Select a trail. 3. Enable data events for the target resources. |
| Best Practices | 1. Regularly review and enable data events for sensitive resources. 2. Use IAM policies to restrict access to critical resources. |
| Compliance | Essential for meeting compliance standards like PCI DSS, HIPAA, or SOC 2. |
| Additional Tools | AWS Config, Security Hub, or third-party monitoring tools for visibility and alerts. |