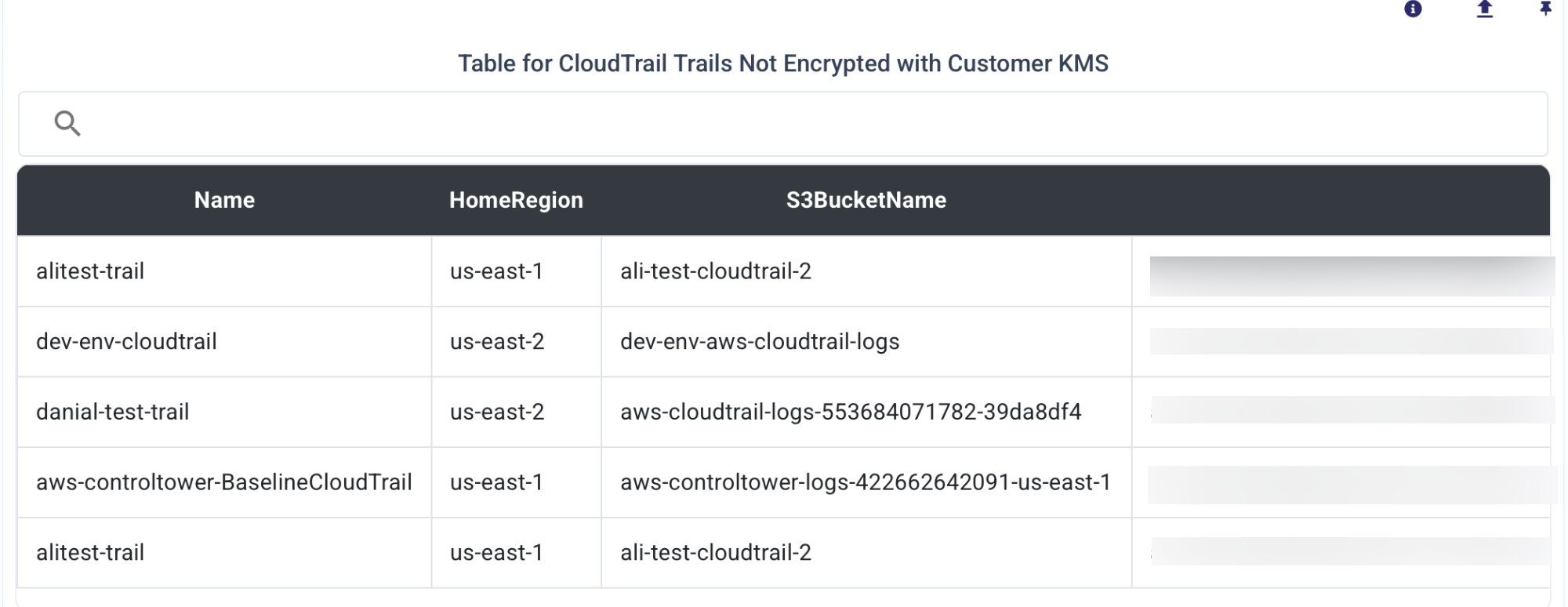
Table for CloudTrail Trails Not Encrypted with Customer KMS
This table provides an overview of important information regarding CloudTrail trails that are not encrypted with a customer-managed KMS key. It is intended for IT and Security Engineers responsible for ensuring compliance and security in cloud environments.
| Aspect | Details |
|---|---|
| Issue | CloudTrail trails are not encrypted using a Customer Managed Key (CMK) from AWS KMS. |
| Impact | Potential exposure of sensitive audit logs to unauthorized access or tampering. |
| Recommended Action | Enable encryption for CloudTrail logs using a CMK to enhance security and access control. |
| Steps to Remediate | 1. Identify CloudTrail trails without CMK encryption. |
| 2. Update the trail configuration to use a CMK for encryption. | |
| 3. Ensure IAM policies allow CloudTrail to access the CMK. | |
| Verification | Use the AWS Management Console, CLI, or SDK to verify CMK encryption status of trails. |
| Tools | AWS Management Console, AWS CLI, AWS Config, Security Hub, or third-party compliance tools. |
| Compliance Standards | Ensures adherence to compliance frameworks such as PCI DSS, HIPAA, and SOC 2. |
| AWS Best Practices | Encrypt CloudTrail logs with a CMK to meet AWS security best practices. |
| Audit Commands | aws cloudtrail describe-trails --query 'trailList[*].KmsKeyID' |
| Log Verification | Check S3 bucket policies and KMS key usage in AWS CloudTrail event history. |
| Alerting | Configure AWS Config Rules or Security Hub findings to monitor non-compliant trails. |