apibom-overview
API BOM Overview
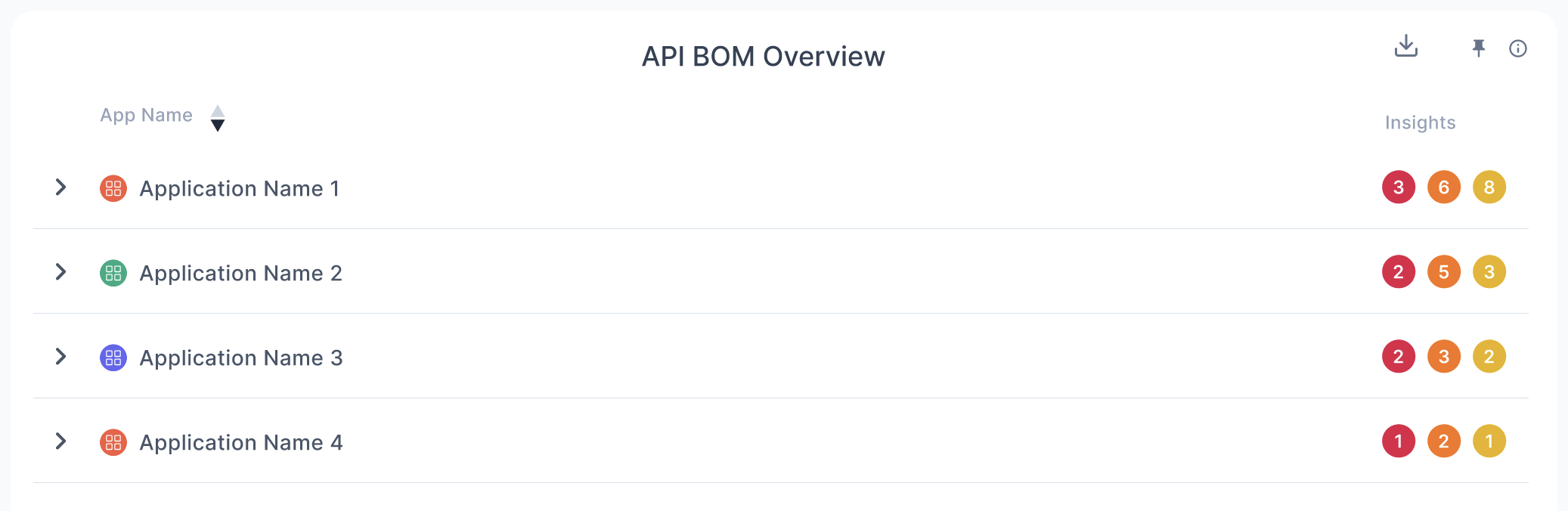
Severity Color Mapping:
- 🔴 Red = Critical vulnerabilities
- 🟧 Orange = High vulnerabilities
- 🟨 Yellow = Medium vulnerabilities
1. Day in the Life of an AppSec Engineer Using This Chart
An AppSec engineer responsible for securing applications and APIs would use this API BOM view to:
-
Start-of-Day API Triage:
- Check which applications and endpoints have critical or high-risk vulnerabilities across APIs.
- In this example, Application Name 1 is top priority with 6 critical vulnerabilities.
-
Remediation Planning:
- Drill down by endpoint, function, and framework (e.g.,
getPerson()in express.js) to prepare targeted fixes or assign tasks to developers.
- Drill down by endpoint, function, and framework (e.g.,
-
Repository-Level Action:
- Uses the repository mapping (e.g.,
user-management) to file JIRA tickets, trigger CI/CD patch workflows, or conduct code reviews.
- Uses the repository mapping (e.g.,
-
Cross-Team Coordination:
- Coordinates with developers and API owners to ensure patches or mitigations are prioritized where multiple vulnerabilities are stacked on a single endpoint.
2. Impact on AppSec Operations
This API BOM breakdown improves precision, prioritization, and accountability in API security operations:
-
API-Centric Vulnerability Management:
- Provides granular visibility into API endpoints, functions, and frameworks tied to known vulnerabilities.
-
Consolidated Risk Context:
- By grouping insights at the app, endpoint, and repo level, security teams can remediate smarter—not just faster.
-
Faster SLA Monitoring and Escalation:
- Enables teams to track how long vulnerabilities persist, identify risky trends, and enforce patching SLAs for APIs.
-
Reusable Fix Strategy:
- Identifies common endpoints or reusable components (e.g.,
/persons/{id}) that are vulnerable across multiple apps, allowing bulk fixes or shared remediations.
- Identifies common endpoints or reusable components (e.g.,
3. What Are the Decisions It Drives?
-
Which apps and endpoints need immediate attention?
- Application Name 1 and the
/persons/{id}endpoint ingetPerson()function have multiple critical vulnerabilities—these are top priority.
- Application Name 1 and the
-
Is the same vulnerable API reused in multiple places?
- Yes—the same API and endpoint is listed multiple times under Application Name 1, likely due to detection duplication or layered insight categorization.
-
Do we need to isolate or temporarily block access to certain APIs?
- Possibly—for example, if
/persons/{id}is public-facing, runtime mitigations like rate limiting, auth hardening, or WAF rules may be needed until patched.
- Possibly—for example, if
-
Which repositories need focused code-level intervention?
- The
user-managementrepository is the source for all vulnerabilities in Application Name 1—it should be triaged and prioritized in development backlog.
- The
-
Are there shared framework concerns?
- Yes—all vulnerabilities stem from endpoints built using express.js, which may indicate framework-specific security gaps or usage patterns.
4. Detailed Description of the Chart
This hierarchical API BOM (Bill of Materials) view maps APIs, endpoints, and related vulnerabilities per application:
| Field | Description |
|---|---|
| App Name | Lists all applications scanned for API-level vulnerabilities. |
| API | The name of the API or service exposing endpoints (e.g., Damn-vulnerable-sca API). |
| Endpoint | Specific API paths (e.g., /persons/{id}) found to be vulnerable. |
| Function | Code-level function handling the endpoint (e.g., getPerson() function). |
| Framework | Tech stack used (e.g., expressjs for Node-based services). |
| Repository | Git repo from which the vulnerable endpoint originates (e.g., user-management). |
| Insights | Severity breakdown per row — 🔴 Critical, 🟧 High, 🟨 Medium vulnerabilities. |
- Applications 2–4 also show a combination of critical to medium-level vulnerabilities but with fewer entries, indicating less immediate risk or fewer detected APIs.
Final Thoughts
This API BOM Overview enables AppSec teams to:
✅ Prioritize remediation by endpoint risk and reuse
✅ Drill down from app to repo to function for actionable fixes
✅ Identify framework or repo patterns contributing to recurring API issues
✅ Improve coordination between AppSec and development teams