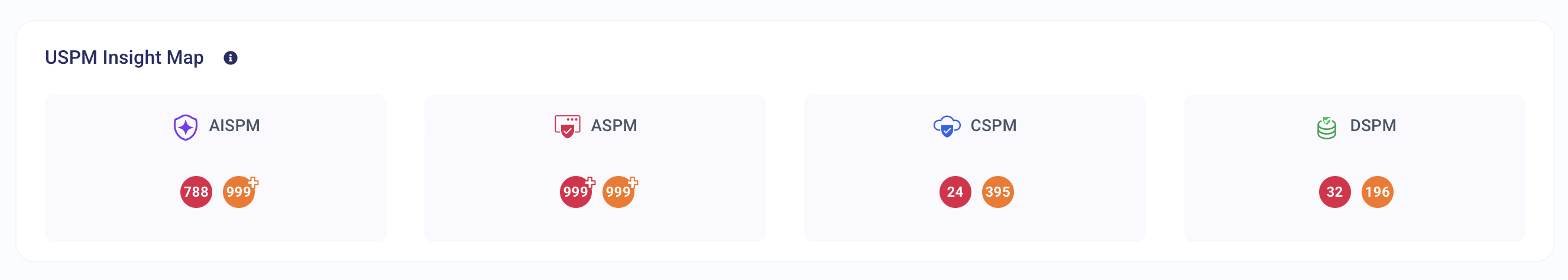
unified-insight-map
Insight Map Chart
1. Day in the Life of an AppSec Engineer Using This Chart
An Application Security (AppSec) Engineer would use this Insight Map to get a holistic view of vulnerabilities across different security domains. Here's how it fits into their daily workflow:
-
Morning Security Review:
- The engineer scans the various security categories (e.g., App Security, Repository Security, IaC Security, Cloud Security) to identify high-risk areas.
- Prioritizes categories with the highest number of critical and high-severity vulnerabilities for immediate remediation.
-
Cross-Team Coordination:
- Engages with DevOps, cloud engineers, and security teams to discuss security risks in different domains.
- Works with developers to fix Code Security and Secrets/PII Security vulnerabilities.
- Collaborates with Cloud and IaC teams to remediate infrastructure-related vulnerabilities.
-
Security Posture Assessment:
- Uses this dashboard to determine whether vulnerabilities are evenly distributed or if certain areas require urgent intervention.
- For example, if IaC Security has 16 high-severity vulnerabilities, the engineer focuses on infrastructure security fixes.
-
Reporting and Compliance Audits:
- Uses this visual breakdown to prepare reports for security leadership, compliance teams, and executive stakeholders.
- Ensures high-risk vulnerabilities (red markers) are resolved before security audits.
2. Impact on AppSec Operations
This chart streamlines vulnerability management by enabling:
-
Risk-Based Prioritization:
- Helps security teams focus on the most critical security categories (e.g., Code Security, Secrets Security, IaC Security) rather than treating all vulnerabilities equally.
-
Improved Cross-Team Security Alignment:
- Encourages collaboration between application developers, DevOps, cloud engineers, and security teams.
- Ensures each domain (App, Code, IaC, Cloud, CI/CD, etc.) has clear accountability for fixing vulnerabilities.
-
Faster Remediation Efforts:
- Categorizing vulnerabilities by security domain allows security teams to tackle issues efficiently without duplicating efforts.
- Example: Instead of fixing vulnerabilities one by one, the team can roll out bulk fixes in the most affected domain first.
-
Security Compliance Readiness:
- Helps track whether security controls are effective across all domains before an ISO 27001, SOC2, PCI-DSS, or NIST compliance audit.
3. What Decisions Does This Chart Drive?
-
Which security category should be prioritized for remediation?
- If Code Security (34 vulnerabilities) and IaC Security (27 vulnerabilities) have the highest number of issues, those areas should be fixed first.
-
Are critical vulnerabilities evenly distributed or concentrated in one area?
- If certain security areas have a disproportionate number of critical risks, teams should investigate systemic security weaknesses in those areas.
-
Do we need to allocate more resources to specific security domains?
- If one area (e.g., Secrets Security) has too many high-risk vulnerabilities, the team might need dedicated security engineers or automated tools.
-
Is our current security strategy balanced across all domains?
- If some categories (e.g., CI/CD Security) have very few vulnerabilities, this could mean:
- The area is well-protected.
- Security testing is inadequate, requiring deeper analysis.
- If some categories (e.g., CI/CD Security) have very few vulnerabilities, this could mean:
-
Which teams should take ownership of fixing vulnerabilities?
- Cloud Security vulnerabilities → Cloud security engineers.
- Code Security vulnerabilities → Application developers.
- Secrets/PII vulnerabilities → DevOps or security engineers.